NYC Department of Health is Spending Taxpayers’ Money to Spy on Racially Profiled Communities Using Federal Intelligence Affiliates as “Private Contractors”
Thanks to this awesome find from Ashmedai, yours truly is a verified card-carrying wrongthinker profiled in several reports by Groupsense.io – a bunch of CIA failures “cybersecurity company” moonlighting for Mordor NYC Health Department among other distinguished wannabe totalitarian customers.
My family are excited, especially my children – mommy is on the government watchlist! I finally have street cred.
Here is a link to the 900-page FOIAed document which collates numerous reports spanning June 3, 2021 to September 26, 2022. I invite my colleagues in the wrongthink community to check if they are on this list, too. I only scanned a few pages and found many familiar names: Drs. Rose, McCullough, Nass, Kory, Ruby, Yeadon, late Dr. Zelenko, Steve Kirsch, Igor Chudov, El Gato Malo as well as The Epoch Times and Children’s Health Defense. Of course, Robert Kennedy Jr. is there, too, with numerous mentions.
Notably, Grpoupsense.io’s intelligence gathering skills are rather mediocre. They don’t always get the names correctly: attorney Todd Callender is on the list as “Tom Callender”, former DEA agent Jeffrey Prather is “Jeremy Prather”, and Ashmedai is misgendered (everyone knows it’s not a “they” but a demon/demonself).
The reports are titled thusly:

“Disinformation cadence”? “NYC Vaccine Command Center”??? Oh, puhleeeze! Do something less cringey next time.
Here is some marketing advice for NYC Health Department: consider adopting this pretty Eye of Sauron flag to communicate that you are watching us, humans who dare to have ideas not endorsed by the lizardpeople.
Or maybe an owl. Or a pyramid. But I digress.
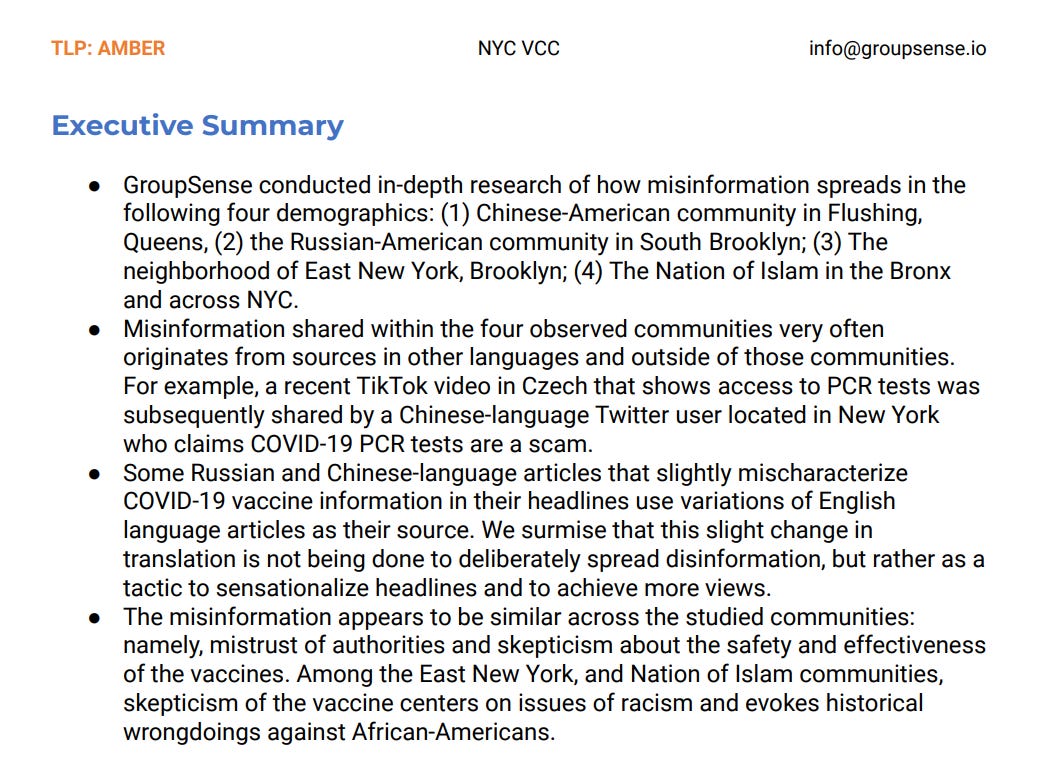
As expected, NYC Health Department aimed to do some racial profiling: Chinese, Russian (mostly Jewish), African-American, Puerto Rican/Latino and Islamic communities were targets of this reconnaissance exercise. There is a bit of self-awareness. “Mistrust of authorities” (from people who escaped communism) and “historical wrongdoings against African-Americans” are of course the reasons to monitor these people by the government!
I was intrigued about the “highly-automated” stasi-on-demand Groupsense.io company and decided to do my own profiling of the profilers.
They advertise themselves as a cybersecurity and digital risk mitigation services company. The website sucks and looks like a fake template. It is immediately apparent that Groupsense is much more concerned with intelligence gathering than handling cyber threats/cybersecurity.
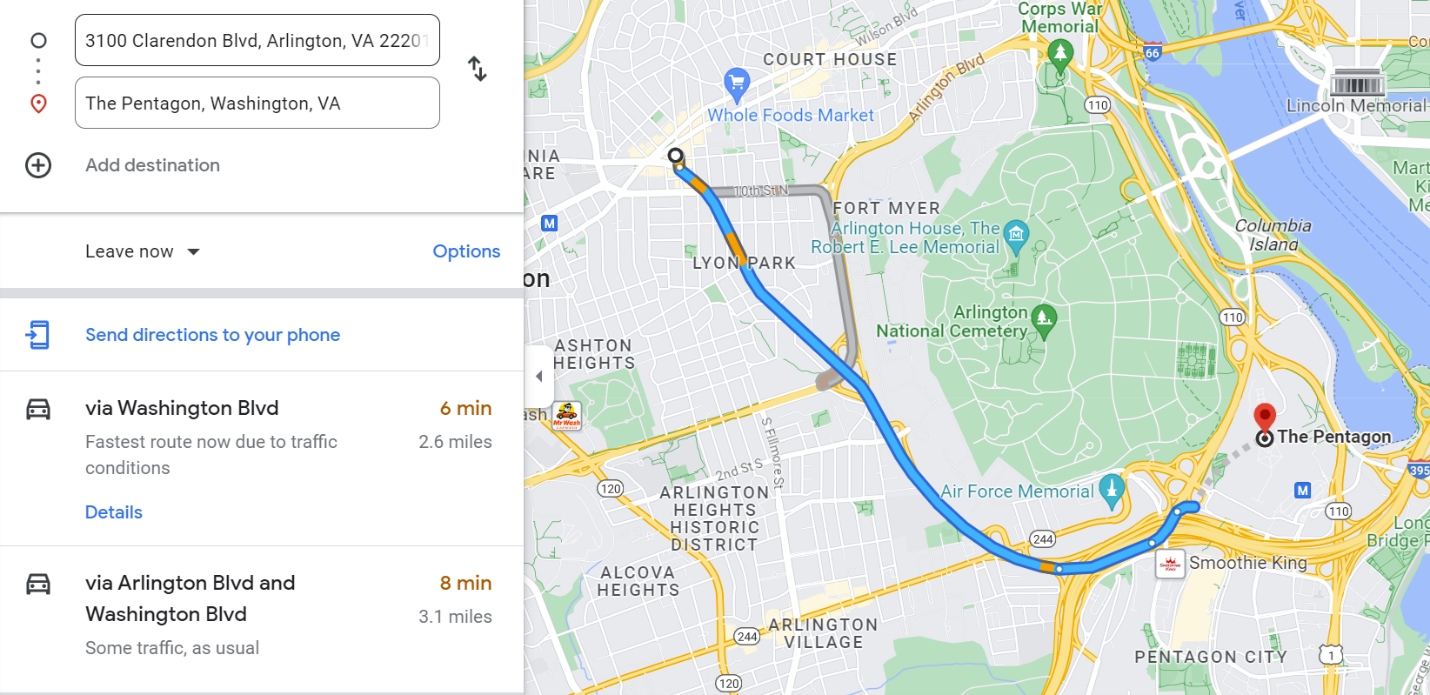
Their office is located at 3100 Clarendon Boulevard in Arlington, VA. For those unfamiliar with the Washington DC geography, that is a 6-minute car ride away from the Pentagon. Totally coincidental.
Let’s look at the business offerings.
Digital Risk Protection Services:
This page at first glance seems to offer clients services that help to mitigate their cyber risk and prevent cyber-attacks. However, upon closer inspection, the page is an advertisement for their intelligence gathering services, which seem to be enabled by a formidable intelligence gathering tool (Tracelight), developed by God-knows-who (we all know who, though).
Automated Collection:
“Tracelight ingests over 500 OSINT (Open-Source Intelligence) sources and covers all major and minor social media networks for complete open web coverage.”
Translation: We have a tool that can keep tabs on media developments from anyone that you (the client) want to monitor and suppress.
Adversary Engagement:
“GroupSense is one of the few vendors that still communicates directly with threat actors using over 1,000 carefully crafted and maintained personas, providing unprecedented protection across the dark web.”
Translation: We make thousands of fake social media accounts to distract and brainwash masses who take social media seriously, and take down unwanted “targets”. It’s for the “dark web”, we swear! And Twitter, Facebook, Instagram, Telegram, LinkedIn, Tik Tock and all others.
Anyone wants to venture a guess how much of the social media is fake CIA bots operated by the likes of Groupsense? But Elon Musk told us there are no more “carefully crafted” personas on Twitter! Riiight.
By the way, there is a version of this Groupsense-like service provider that operates a bunch of bots writing comments to peer reviewed journals and fake Pubpeer website to provide an excuse for them to take down science papers they don’t like. For example, Dr. Sabine Hazan’s peer reviewed and accepted ivermectin hypothesis paper was eliminated from the Frontiers journal with “help” by such service provider.
There are dozens of “companies” like Groupsense out there. Fake “cybersecurity” shops staffed by intelligence/military/government affiliates to enforce the official narrative and take down opposition. The whole internet must be monitored at our expense in case anyone says Mark Milley is too fat.
Here is another interesting service from Groupsense:
Election Threat Protection (it’s not opposition suppression at all! it’s for “cybersecurity”):
18 months prior to an election:
-
Assess the digital threat profile of the organization and the election
-
Identify threats, adversaries, vulnerabilities and high risk issues
-
Advise client on security improvements
-
Commence threat monitoring
30 days prior to an election:
-
Assess the digital threat profile of the organization and the election
-
Identify threats, adversaries, vulnerabilities and high risk issues
-
Advise client on security improvements
-
Commence threat monitoring
On the day of the election:
-
Continuous monitoring before, during and after polls close
-
Real-time monitoring to detect active threats
-
Constant communication with the client security team
Post-election:
-
Monitoring for post-election communications
-
Documenting behavior of threat actors

Meaning, Groupsense not only can provide the information necessary to government officials to target and suppress any opposition, but can do the actual suppression themselves. This is absolutely the kind of work that local and state governments would want outsourced to “private contractors”, as they would be risking too much in the event they are caught doing this themselves.
There is also “VIP Monitoring”:
What “cybersecurity” firm specializes in protecting major political figures, you may wonder? I wonder this, too.
Let’s look at who works at Groupsese.io:
“The team” is heavily connected to the Intelligence and DOD. As an example Bac Tran, now retired, but still sits on the board of directors for Groupsense provides the sales pipeline to the Intelligence Community and the DoD. He spent 20+ year career at Cisco in various sales and service roles in Federal, DOD and Intelligence.
Adam Bregenzer is Groupsense’s designated tech savant handling two technologies he helped develop in the early 2000’s – SAMAEL and Medusa. SAMAEL is “a blackbox gateway that creates a secure, anonymizing transparent firewall, protecting its users from embarrassing public disclosure.” Medusa is “a multi-process, distributed, modular password cracking application written in C and Python.” I am sure those are all kosher cybersecurity applications, but it is interesting that those two things are highlighted: cover up “embarrassing” stuff and crack passwords for hire.
The most interesting person at Groupsense, however, is Bryce Webster-Jacobsen, Director of Intelligence Operations:

“Bryce is the Director of Intelligence Operations at GroupSense. He leads the day-to-day intelligence activities of our Analyst and Research teams, producing finished, tailored intelligence for our clients. Bryce has previously worked in strategic international education initiatives and trained in open-source intelligence.”
As far as his resume is concerned, there is absolutely no mention of where, or when, or how, or by whom Webster-Jacobsen was trained in OSINT collection.

As we can see, Webster-Jacobsen started his career in 2015, hopping from student life department to student life department at various universities. Is this what is meant by “strategic international education initiatives”? He was an agent placed on various campuses to do what exactly – hang out with 20 year-olds indoctrinating them into “strategic initiatives”? Whose strategic initiatives are those?
It’s hard to cast an aging prostitute as an ingenue, and after a while a 40 yo is no longer a convincing “friend” to college sophomores who think he is a boomer. Three years after his job at GWU he is brought in to work on the executive team of Groupsense.io, a “cybersecurity firm,” as the Director of Intelligence Operations. Based on his public resume, he is highly unqualified for this position except that he has been “trained in open-source intelligence” by some unknown third-party organization.
OK, then! Looks like Bryce needs services from his own employer – his persona is not very well crafted and maintained. Too many obvious gaping holes.
In closing, several people expressed concern with my ban on Twitter and offered help reinstating the account. I appreciate you reaching out. I would like to be clear that I am absolutely not and never was interested in Twitter. I was banned on in 2021, and a couple of months ago re-opened “laptop only” account as my phone number has remained banned. I was invited to do a Twitter Space which I couldn’t do anyway from a laptop-only account, but didn’t know this at the time. Despite having gained 6500+ followers in a short time, nobody was seeing my tweets, not even my husband. Twitter suppresses Substack links. The only “engagement” I would get is from the likes of Groupsense.io and their “carefully curated” fake personas, which is entertaining, but I only have so much time, and I certainly don’t have any for the rainbow colored puke that’s the mainstay content there.
Twitter is thoroughly fake. Not only it is infested with Bryce Webster-Jacobsens’ carefully crafted human and computer bots, but as I have written previously, it is now making fake personas of the content creators who have signed up to its “subscription” platform.
My little experiment with it demonstrates that the Monster’s strategy with regard to social media has changed. Before they banned any descent from the narrative. They realized that that was not workable, and only rapidly grew alternative platforms (where we all met, connected and rejoiced). The cabal then decided that we need to be brough back for surveillance via “more open and inclusive Twitter committed to free speech”. Thus Musk was “allowed” to buy it and pretend openness for a couple of months and even transfer Tucker Carlson from Fox. Please understand all of this is only so that you go back there in hopes of “getting the message out” which is heard by no one other then Groupsense.io and their ilk.
To note, alternative platforms like Telegram are also infested by Bryces and his friends but to a much lesser degree as they have to pretend much harder. I have not noticed much of this on Substack (yet).
I played with a few “cybersecurity” serfs on Twitter a little too hard (and I thank them as it was very entertaining for me!) but their fragile little egos broke. They only ban you when they realize they cannot control you.